How to set up an SSH Honeypot (low interaction) and live stream it
I recently found a streamer on twitch that had an interesting title:
Watch people trying to hack my computer
and the stream was just an endless list of unsuccessful login attempts to the bespoken server. In the description it said:
Can you teach me how to do this? No.
So naturally I had to do a bit of research and try out streaming some failed SSH login attempts into one of my servers. In this post we'll have a look at how to set up your own honeypot with pshitt and if you're interested you can stream the attempts to twitch as well ;)
What's an SSH Honeypot?
A honeypot is a system deliberately left vulnerable to attract attackers in order to find out who they are, how to block/ban them or to harvest their tools and exploits. Think of it as a tool for cyber counter-espionage.
SSH honeypots exist in different categories, high, medium and low interaction.
In a high interaction system (don't do this on your production server), you can just set the root password to password and wait for the show to start. You're basically giving the attackers free reign over a system and will check what they did later.
A medium interaction system puts successful logins into a sandbox or containerised environment that you can investigate later, but that doesn't pose any threat to the host system and can still be blocked from being turned into a spam email server.
A low interaction environment does typically not allow the attacker to execute commands, but merely records their login attempts.
Setup on your Server
If you need a Linux server to try all this out on, you can check out the following providers with some starting credit through some referral codes:
- Digital Ocean with 50$ starting credit
- Vultr with 50$ starting credit
- Linode with 20$ starting credit
We'll install pshitt and let it run on port 22, the default SSH port in order to record a reasonable amount of username/passwords combinations.
First, however, assuming you'll run this on a linux vps, you'll probably need to change the port that your actual sshd server is running on, which is a good security practise anyways.
On Debian/Ubuntu and the like your config file for that will be at /etc/ssh/sshd_config and you'll need to remove the # before Port and change the port to something like 5623 or another unexpected and not commonly used port.
-#Port 22
+Port 5623
#AddressFamily any
#ListenAddress 0.0.0.0
#ListenAddress ::
After the change, restart the server with service ssh restart. If you have an ssh config for your server, remember you can specify a port to connect to it, you don't actually need to remember that port. An example from my ~/.ssh/config:
Host misery
HostName 1.1.1.1
Port 5623
User root
IdentitiesOnly yes
IdentityFile ~/.ssh/skeleton-key
For the next step we need to make sure we have python and git installed:
apt install git python2.7 python-pip
Alright, now that we've freed up the port, we need to start listening for login attempts, for that we'll install pshitt by cloning the git repository:
git clone https://github.com/regit/pshitt.git
cd pshitt
pip install paramiko
Now we can create a small script that will keep the passwords coming, even when we log out of the server. Let's call it listen.sh and paste the following content into it:
./pshitt -o passwords.json -p 22 &
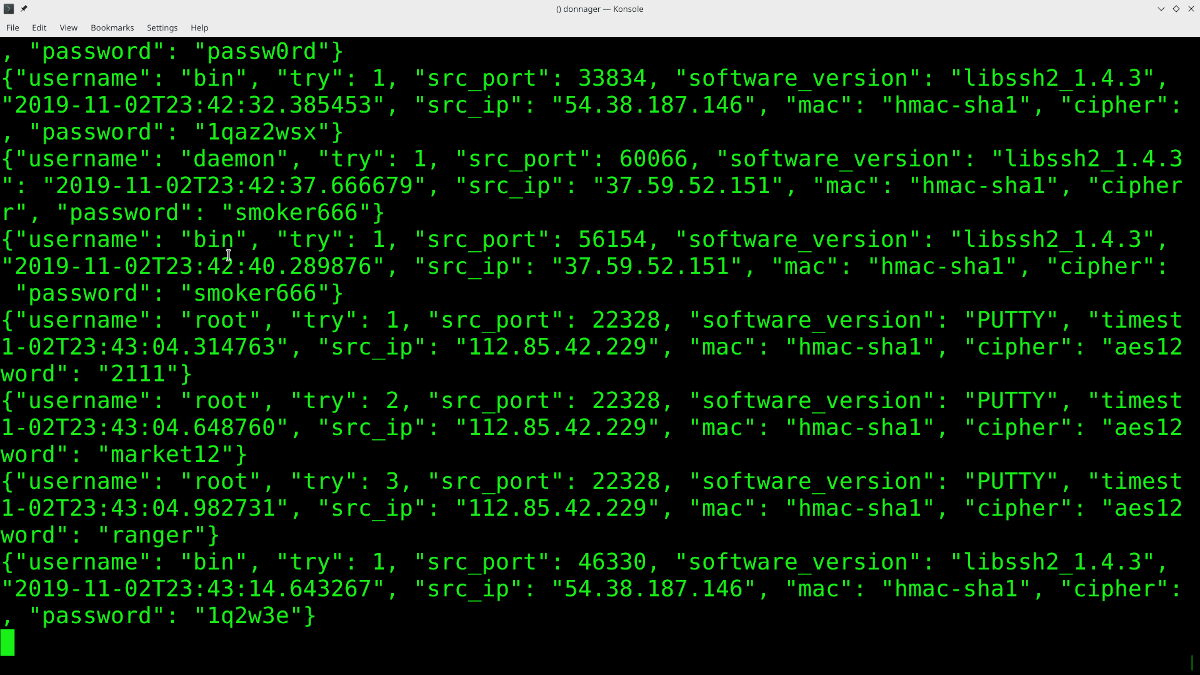
Alright, now you can start your ssh honeypot with ./listen.sh and to see the passwords rushing into your neat little collection you can run: tail -f passwords.json.
If you server has not been used as a web server or similar before, it might take a while for the first requests to come in, but the format should be similar to this:
{"username": "com", "try": 1, "src_port": 64373, "software_version": "libssh-0.6.3", "timestamp": "2019-11-03T00:10:00.131880", "src_ip": "61.12.67.133", "mac": "hmac-sha1", "cipher": "aes256-ctr", "password": "root"}
{"username": "oracle", "try": 1, "src_port": 53767, "software_version": "libssh2_1.4.3", "timestamp": "2019-11-03T00:10:03.781293", "src_ip": "54.38.187.146", "mac": "hmac-sha1", "cipher": "aes128-ctr", "password": "12345678"}
{"username": "oracle", "try": 1, "src_port": 38033, "software_version": "libssh2_1.4.3", "timestamp": "2019-11-03T00:10:49.489394", "src_ip": "54.38.187.146", "mac": "hmac-sha1", "cipher": "aes128-ctr", "password": "123456789"}
{"username": "oracle", "try": 1, "src_port": 50526, "software_version": "libssh2_1.4.3", "timestamp": "2019-11-03T00:11:35.561635", "src_ip": "54.38.187.146", "mac": "hmac-sha1", "cipher": "aes128-ctr", "password": "password"}
{"username": "oracle", "try": 1, "src_port": 34793, "software_version": "libssh2_1.4.3", "timestamp": "2019-11-03T00:12:21.597303", "src_ip": "54.38.187.146", "mac": "hmac-sha1", "cipher": "aes128-ctr", "password": "p@ssw0rd"}
{"username": "oracle", "try": 1, "src_port": 47292, "software_version": "libssh2_1.4.3", "timestamp": "2019-11-03T00:13:06.689592", "src_ip": "54.38.187.146", "mac": "hmac-sha1", "cipher": "aes128-ctr", "password": "p@ssword"}
If you get an error about command python not found, just change the first line of the pshitt script to #!/usr/bin/env python2.7.
Legal Advice
Disclaimer: This isn't actually legal advice, since I'm not a lawyer.
Make sure not to reveal any private data in your research. Technically IP addresses can be considered private, even if they belong to some botnet-machine in China.
Summary
That's how you can set up a simple ssh honey pot that will give you a collection of username/password combos and enable you to block bad actor IP addresses. If you want to stream the output of your terminal, I recommend you use OBS, because it's an awesome and open source piece of software that you can selectively not only stream screens, but also windows with. If you're curious for more, stop by my twitch channel.